Unlocking the Power of Healthcare Contact Centers: Enhancing Patient Care in the Digital Age
InMoment XI
APRIL 24, 2024
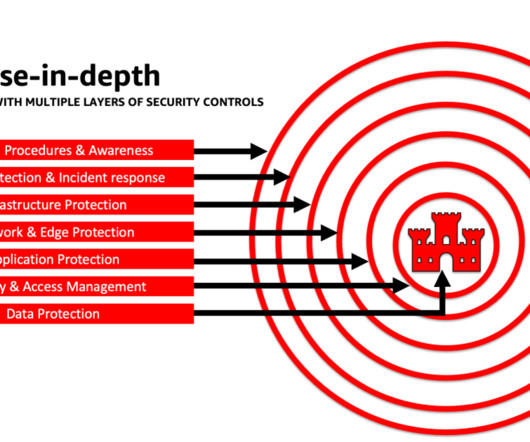
Here are some key factors to consider when evaluating healthcare contact center software: HIPAA Compliance : Given the sensitive nature of healthcare data, it’s essential to choose a software solution that complies with HIPAA regulations to ensure the confidentiality and security of patient information.

















































Let's personalize your content