AWS Machine Learning Blog
Onboard users to Amazon SageMaker Studio with Active Directory group-specific IAM roles
November 2023: This post was updated to include the Amazon SageMaker APIs.
Amazon SageMaker Studio is a web-based integrated development environment (IDE) for machine learning (ML) that lets you build, train, debug, deploy, and monitor your ML models. For provisioning Studio in your AWS account and Region, you first need to create an Amazon SageMaker domain—a construct that encapsulates your ML environment. More concretely, a SageMaker domain consists of an associated Amazon Elastic File System (Amazon EFS) volume, a list of authorized users, and a variety of security, application, policy, and Amazon Virtual Private Cloud (Amazon VPC) configurations.
When creating your SageMaker domain, you can choose to use either AWS IAM Identity Center (successor to AWS Single Sign-On) or AWS Identity and Access Management (IAM) for user authentication methods. Both authentication methods have their own set of use cases; in this post, we focus on SageMaker domains with IAM Identity Center, or single sign-on (SSO) mode, as the authentication method.
With SSO mode, you set up an SSO user and group in IAM Identity Center and then grant access to either the SSO group or user from the Studio console. Currently, all SSO users in a domain inherit the domain’s execution role. This may not work for all organizations. For instance, administrators may want to set up IAM permissions for a Studio SSO user based on their Active Directory (AD) group membership. Furthermore, because administrators are required to manually grant SSO users access to Studio, the process may not scale when onboarding hundreds of users.
In this post, we provide prescriptive guidance for the solution to provision SSO users to Studio with least privilege permissions based on AD group membership. This guidance enables you to quickly scale for onboarding hundreds of users to Studio and achieve your security and compliance posture.
Solution overview
The following diagram illustrates the solution architecture.
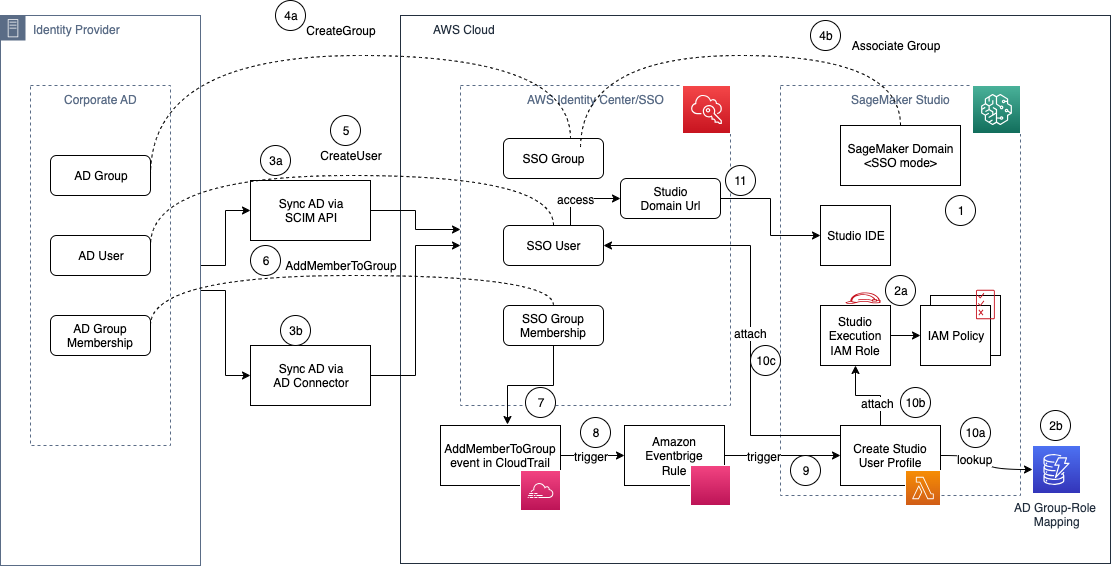
The workflow to provision AD users in Studio includes the following steps:
- Set up a Studio domain in SSO mode.
- For each AD group:
- Set up your Studio execution role with appropriate fine-grained IAM policies
- Record an entry in the AD group-role mapping Amazon DynamoDB table.
Alternatively, you can adopt a naming standard for IAM role ARNs based on the AD group name and derive the IAM role ARN without needing to store the mapping in an external database.
- Sync your AD users and groups and memberships to AWS Identity Center:
- If you’re using an identity provider (IdP) that supports SCIM, use the SCIM API integration with IAM Identity Center.
- If you are using self-managed AD, you may use AD Connector.
- When the AD group is created in your corporate AD, complete the following steps:
- Create a corresponding SSO group in IAM Identity Center.
- Associate the SSO group to the SageMaker domain using APIs.
- When an AD user is created in your corporate AD, a corresponding SSO user is created in IAM Identity Center.
- When the AD user is assigned to an AD group, an IAM Identity Center API (CreateGroupMembership) is invoked, and SSO group membership is created.
- The preceding event is logged in AWS CloudTrail with the name
AddMemberToGroup. - An Amazon EventBridge rule listens to CloudTrail events and matches the
AddMemberToGrouprule pattern. - The EventBridge rule triggers the target AWS Lambda function.
- This Lambda function will call back IAM Identity Center APIs, get the SSO user and group information, and perform the following steps to create the Studio user profile (CreateUserProfile) for the SSO user:
- Look up the DynamoDB table to fetch the IAM role corresponding to the AD group.
- Create a user profile with the SSO user and the IAM role obtained from the lookup table.
- The SSO user is granted access to Studio.
- The SSO user is redirected to the Studio IDE via the Studio domain URL.
Setup for Step 4b: Associate the SSO group to the SageMaker domain using APIs
- Call the Describe Domain API to fetch
SingleSignOnApplicationArnand then call CreateApplicationAssignment passing the retrievedSingleSignOnApplicationArnand the IdC group id that needs to be associated. - If you created the Studio domain before October 1st, 2023, then you need to perform Step 4b manually. This step requires an admin using the SageMaker console at the SageMaker domain level to associate the SSO group to SageMaker domain.
Set up a Lambda function to create the user profiles
The solution uses a Lambda function to create the Studio user profiles. We provide the following sample Lambda function that you can copy and modify to meet your needs for automating the creation of the Studio user profile. This function performs the following actions:
- Receive the CloudTrail
AddMemberToGroupevent from EventBridge. - Retrieve the Studio
DOMAIN_IDfrom the environment variable (you can alternatively hard-code the domain ID or use a DynamoDB table as well if you have multiple domains). - Read from a dummy markup table to match AD users to execution roles. You can change this to fetch from the DynamoDB table if you’re using a table-driven approach. If you use DynamoDB, your Lambda function’s execution role needs permissions to read from the table as well.
- Retrieve the SSO user and AD group membership information from IAM Identity Center, based on the CloudTrail event data.
- Create a Studio user profile for the SSO user, with the SSO details and the matching execution role.
Note that by default, the Lambda execution role doesn’t have access to create user profiles or list SSO users. After you create the Lambda function, access the function’s execution role on IAM and attach the following policy as an inline policy after scoping down as needed based on your organization requirements.
Set up the EventBridge rule for the CloudTrail event
EventBridge is a serverless event bus service that you can use to connect your applications with data from a variety of sources. In this solution, we create a rule-based trigger: EventBridge listens to events and matches against the provided pattern and triggers a Lambda function if the pattern match is successful. As explained in the solution overview, we listen to the AddMemberToGroup event. To set it up, complete the following steps:
- On the EventBridge console, choose Rules in the navigation pane.
- Choose Create rule.
- Provide a rule name, for example,
AddUserToADGroup. - Optionally, enter a description.
- Select default for the event bus.
- Under Rule type, choose Rule with an event pattern, then choose Next.
- On the Build event pattern page, choose Event source as AWS events or EventBridge partner events.
- Under Event pattern, choose the Custom patterns (JSON editor) tab and enter the following pattern:
- Choose Next.
- On the Select target(s) page, choose the AWS service for the target type, the Lambda function as the target, and the function you created earlier, then choose Next.
- Choose Next on the Configure tags page, then choose Create rule on the Review and create page.
After you’ve set the Lambda function and the EventBridge rule, you can test out this solution. To do so, open your IdP and add a user to one of the AD groups with the Studio execution role mapped. Once you add the user, you can verify the Lambda function logs to inspect the event and also see the Studio user provisioned automatically. Additionally, you can use the DescribeUserProfile API call to verify that the user is created with appropriate permissions.
Supporting multiple Studio accounts
To support multiple Studio accounts with the preceding architecture, we recommend the following changes:
- Set up an AD group mapped to each Studio account level.
- Set up a group-level IAM role in each Studio account.
- Set up or derive the group to IAM role mapping.
- Set up a Lambda function to perform cross-account role assumption, based on the IAM role mapping ARN and created user profile.
Deprovisioning users
When a user is removed from their AD group, you should remove their access from the Studio domain as well. With SSO, when a user is removed, the user is disabled in IAM Identity Center automatically if the AD to IAM Identity Center sync is in place, and their Studio application access is immediately revoked.
However, the user profile on Studio still persists. You can add a similar workflow with CloudTrail and a Lambda function to remove the user profile from Studio. The EventBridge trigger should now listen for the DeleteGroupMembership event. In the Lambda function, complete the following steps:
- Obtain the user profile name from the user and group ID.
- List all running apps for the user profile using the ListApps API call, filtering by the
UserProfileNameEqualsparameter. Make sure to check for the paginated response, to list all apps for the user. - Delete all running apps for the user and wait until all apps are deleted. You can use the DescribeApp API to view the app’s status.
- When all apps are in a Deleted state (or Failed), delete the user profile.
With this solution in place, ML platform administrators can maintain group memberships in one central location and automate the Studio user profile management through EventBridge and Lambda functions.
The following code shows a sample CloudTrail event:
The following code shows a sample Studio user profile API request:
Conclusion
In this post, we discussed how administrators can scale Studio onboarding for hundreds of users based on their AD group membership. We demonstrated an end-to-end solution architecture that organizations can adopt to automate and scale their onboarding process to meet their agility, security, and compliance needs. If you’re looking for a scalable solution to automate your user onboarding, try this solution, and leave you feedback below! For more information about onboarding to Studio, see Onboard to Amazon SageMaker Domain.
About the authors
 Ram Vittal is an ML Specialist Solutions Architect at AWS. He has over 20 years of experience architecting and building distributed, hybrid, and cloud applications. He is passionate about building secure and scalable AI/ML and big data solutions to help enterprise customers with their cloud adoption and optimization journey to improve their business outcomes. In his spare time, he rides his motorcycle and walks with his 2-year-old sheep-a-doodle!
Ram Vittal is an ML Specialist Solutions Architect at AWS. He has over 20 years of experience architecting and building distributed, hybrid, and cloud applications. He is passionate about building secure and scalable AI/ML and big data solutions to help enterprise customers with their cloud adoption and optimization journey to improve their business outcomes. In his spare time, he rides his motorcycle and walks with his 2-year-old sheep-a-doodle!
 Durga Sury is an ML Solutions Architect in the Amazon SageMaker Service SA team. She is passionate about making machine learning accessible to everyone. In her 4 years at AWS, she has helped set up AI/ML platforms for enterprise customers. When she isn’t working, she loves motorcycle rides, mystery novels, and hiking with her 5-year-old husky.
Durga Sury is an ML Solutions Architect in the Amazon SageMaker Service SA team. She is passionate about making machine learning accessible to everyone. In her 4 years at AWS, she has helped set up AI/ML platforms for enterprise customers. When she isn’t working, she loves motorcycle rides, mystery novels, and hiking with her 5-year-old husky.